Some of you maybe noticed, that the option Send to –> Mail recipient in the context menu from Windows 10 (several Builds) can cause crashing the File Explorer.
This is in combination with Office365 and Click-To-Run as the application is based on an App-V technology. The bug is not new and should really be fixed in a next CU of Windows 10, please MS. There is a very easy fix for that. Use a registry key to get it sorted. This is tested on many Windows 10 Enterprise 1709 Build.
Registry Key value:
*******************************************************************
Windows Registry Editor Version 5.00
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\ClickToRun\OverRide]
“AllowJitvInAppvVirtualizedProcess”=dword:00000001
*******************************************************************
As always: Be careful when you do changes in the registry.
Copy the value from the reg key above to a notepad and save it as “FixSendToMail.reg”. Double click the reg file and import ist to the client with the issue. This will fix it immediately.
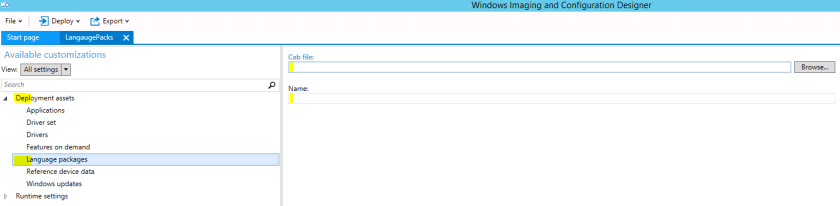
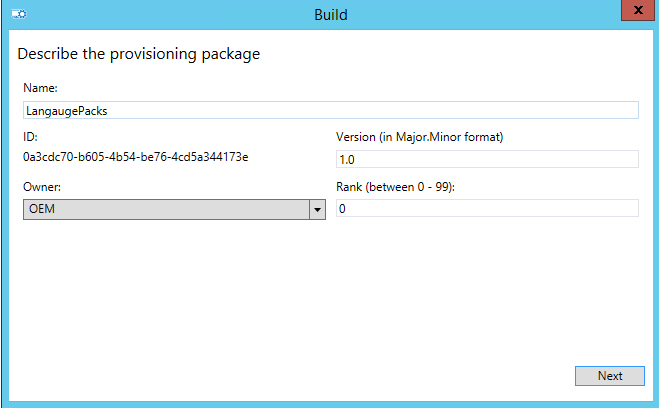
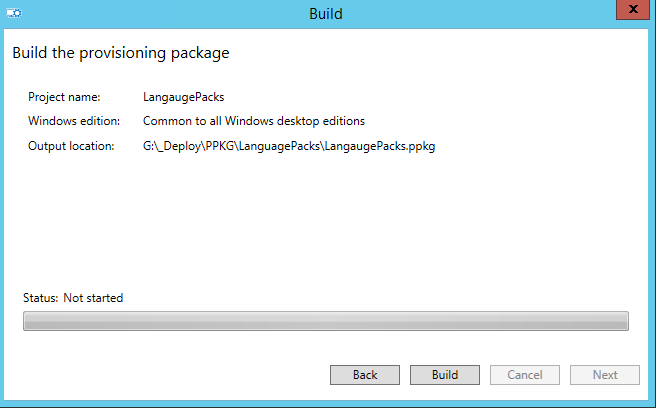
You can also add this step directly in your ConfigMgr Tasksequence. Just make sure you add the step after installing Office365. Use the reg key above and add it to your Customization Package for Windows 10.
Run a command line step in your Tasksequence by using the command bellow:
*******************************************************************
regedit.exe /s FixSendToMail.reg
*******************************************************************
Hope this helps.
Cheers, Al





![sccm2012_logo.gif-1200x0[1]](https://blog.alschneiter.com/wp-content/uploads/2015/10/sccm2012_logo-gif-1200x01.png?w=300&h=160)