I have recently faced following issue “HTTP test request failed, status code is 403. “Forbidden” ” on Management Point and was not Abel to connect MAC OSx Devices to the MP. To fix this issue, I followed the below steps and maybe you can do so.
Issue
We have HTTPS enabled on the Management Point for managing MAC OSx Clients and it is still not able authenticate. Due to this it is reporting this error.
The MPControl.log is reporting following error:
“Call to HttpSendRequestSync failed for port 443 with status code 403, text: Forbidden” “HTTP test request failed, status code is 403. ‘Forbidden”

Solution
Look at the IIS Log files under your inetpub folder for more details of the error. The log files are located under (C or D drive) \inetpub\logs\Logfiles\W3SVC1
As you see in the below highlighted line error code 403 13, which indicates an issue with Client Certificate Revocation (CRL) Check on IIS.

To fix this issue disable the Revocation check. Client Certificate Revocation is enabled by default. We need to delete all existing bindings on IIS and readd them again. The easiest way to do this is using the netsh command.
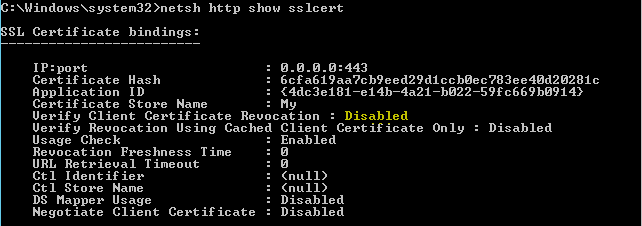
- Run the below command line and make a note of the details
netsh http show sslcert

- Delete existing SSL bindings
netsh http delete sslcert ipport=0.0.0.0:443

- Readd SSL binding and disable CRL check
netsh (enter)
http add sslcert ipport=0.0.0.0:443 certhash= 6cfa619aa7cb9eed29d1ccb0ec783ee40d20281c appid={4dc3e181-e14b-4a21-b022-59fc669b0914} certstorename=My verifyclientcertrevocation=disable

- Run “netsh http show sslcert” again to check the status of the CRL check
- Check the mpcontrol.log. The error is gone.
Tray again to connect your MAC OSx ConfigMgr Client to your ConfigMgr Primary Site Server. You should now be able to connect. Your MAC will also appear in the ConfigMgr console.
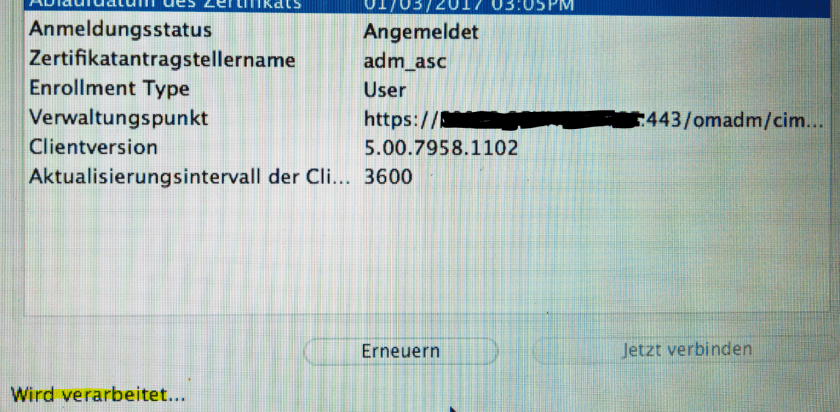
Connection to ConfigMgr established:

Now manage your MAC under “Devices” in the ConfigMgr Console:

Use this as a workaround if you’re not able to publish the CRL for your Site Servers.
Enjoy ConfigMgr!
