Recently a customer called, that the Automatic Enrollment for MDM is not working as excepted and the clients are getting some errors during MDM Autoenrollment. Easy I thought, let’s have a look…
Within the Eventlog under Microsoft-Windows-DeviceManagement-Enterprise-Diagnostics-Provider the error Unknown Win32 Error code: 0x80180001 was triggerd.
Usually you configure MDM Automatic enrollment using a GPO after your devices are Hybrid Joined (to do so, check that post here).
Since Windows 10 1903 this GPO policy got a change. You can now select Device or User Authentication. If you select Device Authentication, a device token will be used to enroll the device, but this is not supported for Intune, based on this Docs article.
Also, another error caused in the Eventlog which indicates, that the GPO setting must be misconfigured:
MDM Enroll: Server Returned Fault/Code/Subcode/Value=(MessageFormat) Fault/Reason/Text=(Device based token is not supported for enrollment type OnPremiseGroupPolicyCoManaged
As soon this GPO policy is applied to a device, a scheduled task is created and triggers the enrollment process every 5 minutes.
You can find this task under \Microsoft\Windows\EnterpriseMgmt. If you check the arguments for this specific task, you probably realize that the argument uses the string:
/c /AutoEnrollMDMUsingAADDeviceCredential
So, still device authentication is used. This causes our error. Let’s change that to User authentication.
To test the enrollment with user auth, you can ether changing the GPO to user authentication (this did not change the scheduled task arguments in my case, even after reboots, gpupdate, etc.) or just manually changing the string to:
/c /AutoEnrollMDMUsingAADUserCredential
After that, the devices started to auto enroll into Intune. Be aware, that auto enrollment, enrollment restriction and Azure AD device registration needs to be enabled and configured for that.
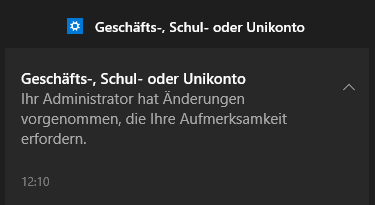
Your users will receive a toast message that some account settings has been changed.
If you use Azure MFA maybe another error will popup in the event log but not displayed to the enduser:
Auto MDM Enroll: Failed (Unknown Win32 Error code: 0x8018002a)
This will also block the enrollment process. You can avoid that, by configuring an exclusion in Conditional Access for the “Microsoft Intune Enrollment” cloud app.
Hope this helps!

This was really helpful. Thanks and keep up the useful content
LikeLiked by 1 person
Thank you. This worked for me as well
LikeLike
Glad it helped! Cheers, Al
LikeLike
Hey Al,
How did you add the User credential
/c /AutoEnrollMDMUsingAADUserCredential
This to Task scheduler and how?
LikeLike
Hi HJ,
you can use GPO to achieve this. You can follow this link:
https://docs.microsoft.com/en-us/windows/client-management/mdm/enroll-a-windows-10-device-automatically-using-group-policy
Regards,
Al
LikeLike
Great content, thank you for sharing! This was invaluable in troubleshooting my Hybrid deployment.
LikeLike
Thank you Ted
LikeLike
Thank you very much ! I got the 0x80180001 on 2 devices.
The first succeeded to join using the user credentials. I didn’t notice at first the disclaimer of Microsoft saying that the device credentials is used in a co-managed environment.
The second, I had the 0x8018000a error and I had to delete all Enrollments ID under HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Enrollments
LikeLike
What’s the full conditional access policy settings you are using? I tried and it was not working, I had to whitelist the external IP in MFA to get this working on hybrid joined with MFA turned on.
LikeLike
Hi Dan, in this case where we had that issue, no CA was in place for the enrollment.
LikeLike
Al,
Thanks. The CA for some reason is not working. What did you put in for Grant or Session section then?
LikeLike